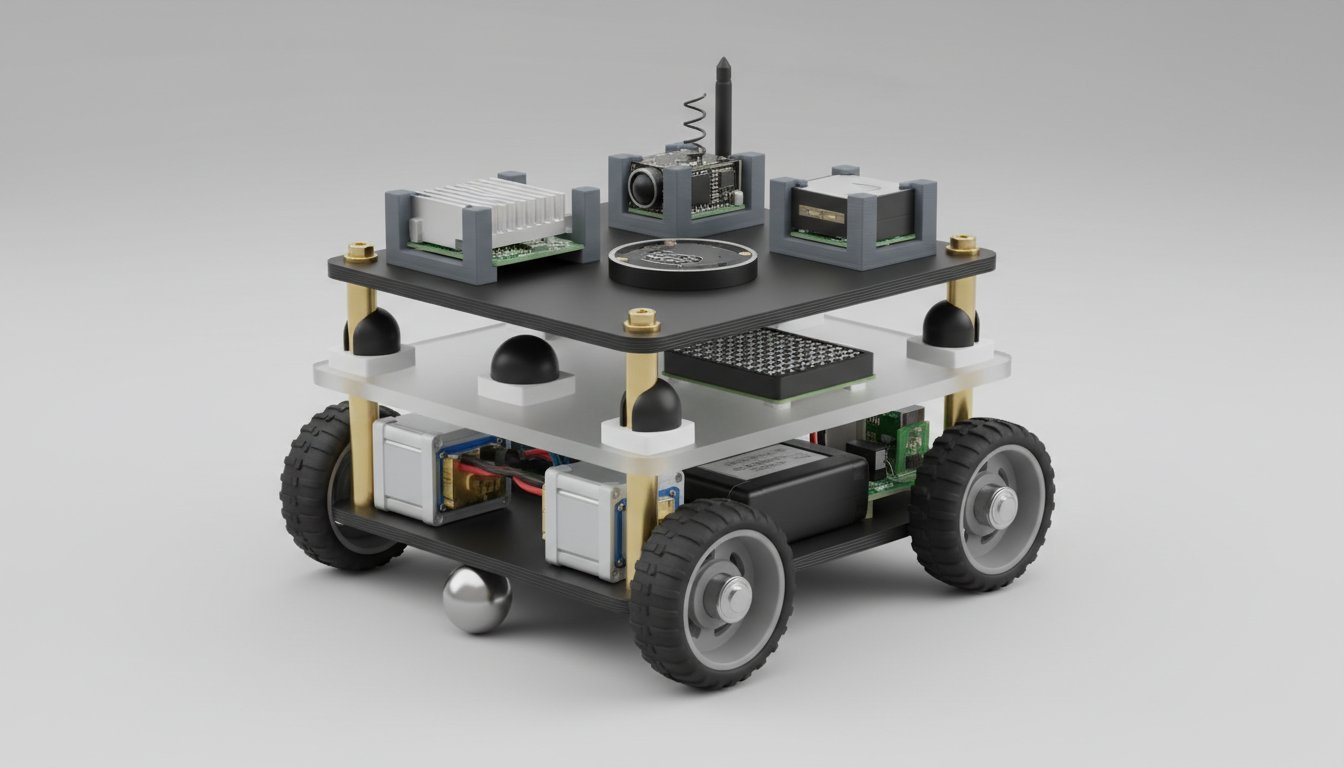
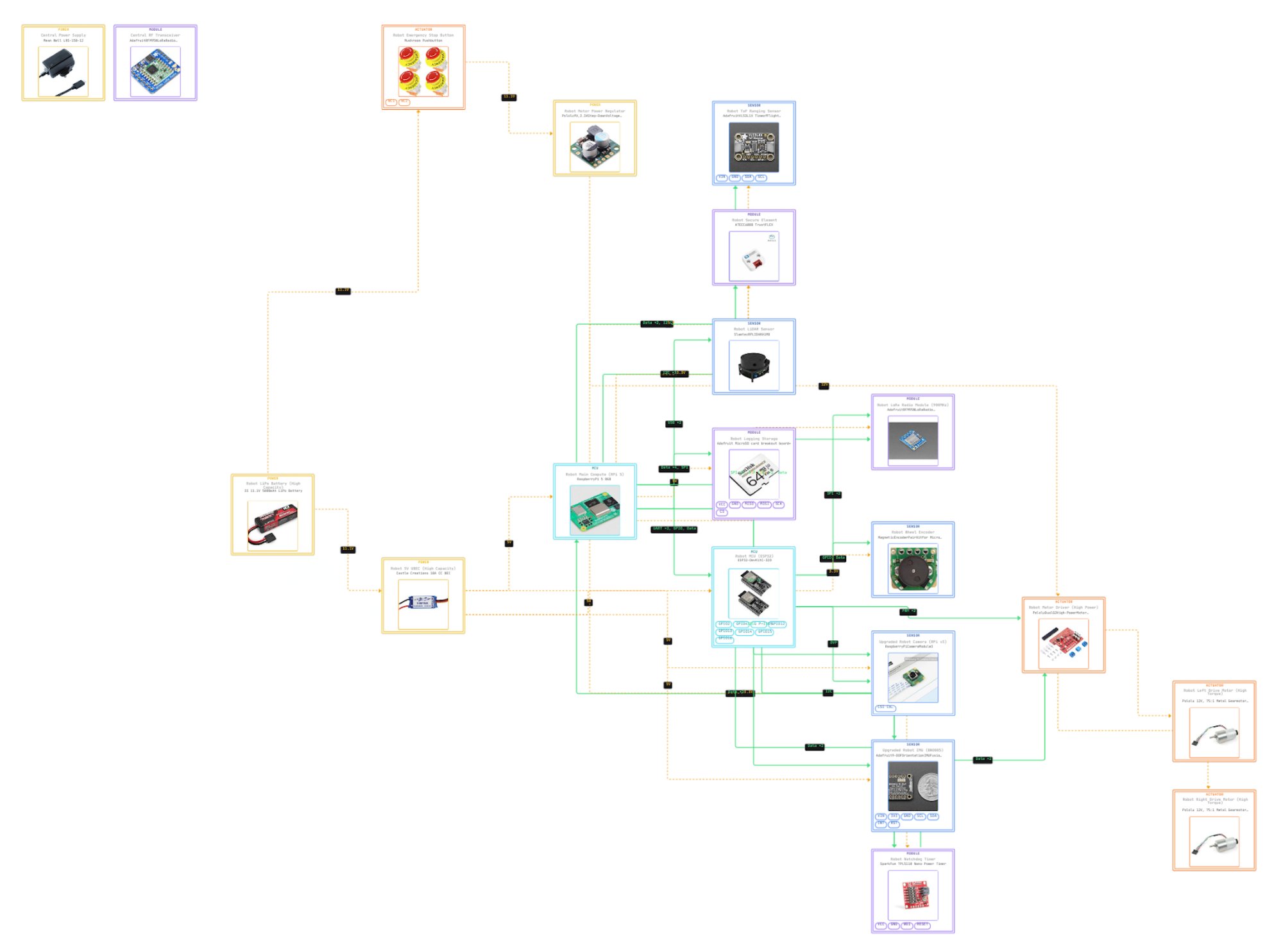
Authority-Governed Assured Autonomy Rover Testbed
A research platform implementing SATA trust evaluation, HMAA mission authority control, and CARA recovery enforcement for resilient autonomous systems. The testbed enables controlled experiments on autonomy degradation, sensor trust evaluation, and mission recovery under contested operating conditions. The broader research program also extends these governance principles to manipulation systems, including authority-controlled robotic arms.
This platform represents an implemented experimental system integrating hardware architecture, governance software, and simulation-based validation. This testbed is part of a unified research framework for authority-governed autonomous systems spanning single-agent, multi-agent, and manipulation domains.
Design Complete · Implementation In ProgressKey Contributions
- Governance architecture for trust-aware autonomous systems
- Authority control framework for degraded autonomy environments
- Experimental testbed for adversarial sensor failure scenarios
- Interactive simulation platform for autonomy safety validation
- Reproducible research platform under $500
- Extensible governance framework applicable to both autonomous navigation and robotic manipulation
Zenodo Publication: Oktenli, B. (2026). Authority-Governed Assured Autonomy Rover Testbed: System Architecture, Governance Design, and Reproducible Artifact Package (v1.0). Zenodo. https://doi.org/10.5281/zenodo.19143190