Burak Oktenli
Developing governance architectures intended to enable safe, accountable, and controllable deployment of autonomous systems in critical infrastructure, national security, and safety-critical autonomous environments. These architectures function as control layers governing how authority is granted, restricted, and recovered within autonomous systems. This work focuses on authority lifecycle control, decision integrity, and fail-safe recovery mechanisms that maintain human oversight in high-speed human-machine environments.
This research integrates physical testbeds, simulation platforms, and formal architectural design.
Research status: All four patent applications are provisional (awaiting USPTO action). All 33 publications are open-access preprints or published papers. All hardware platforms are research demonstrators at TRL 2-4, not commercial products.
Here's the right starting point.
This site serves different audiences with different needs. Pick the role that best describes you.
Research Mission
The Problem. Autonomous systems in defense and civilian transportation make decisions faster than humans can intervene, yet no standardized architecture enforces real-time authority governance. DoD Directive 3000.09 requires human control over autonomous weapons but lacks a technical enforcement mechanism. Nearly 40,000 Americans die annually in traffic crashes; NHTSA has documented 1,429 AV incidents (2021-2025); and the SELF DRIVE Act of 2026 (H.R. 7390) now mandates cybersecurity plans for "false vehicle control commands", but no validated reference architecture exists to implement these requirements.
The Gap. Policy frameworks (NIST AI RMF) establish principles but do not enforce them in hardware. Planning-layer safety systems (Mobileye RSS, NVIDIA SFF, SOTIF) constrain behavior but do not govern whether commands reach actuators. Software-only monitors can be bypassed. What is missing: a hardware-enforced architectural layer that continuously evaluates sensor trust, computes graded authority, enforces deliberation windows, and cuts actuator authority through a fail-safe when trust degrades, deterministically, in real-time, without firmware involvement.
My Contribution. Seven governance architectures managing the full authority lifecycle: trust evaluation, authority computation, command gating, consensus, deliberation, deception detection, and recovery:
- SATA: Sensor trust attestation using weighted Dempster-Shafer fusion with cross-sensor validation (Patent: U.S. Provisional 64/002,453)
- HMAA: Four-level authority computation (A3-A0) with asymmetric hysteresis: immediate downgrade, 5-15s delayed upgrade (Patent: 63/999,105)
- CARA: Deterministic GREP-phase recovery: Govern → Restrict → Execute → Persist, with mutual exclusion (Patent: 64/000,170)
- MAIVA: Byzantine fault-tolerant multi-agent consensus with CUSUM-augmented anomaly detection
- FLAME: Mandatory deliberation windows preventing safety-critical actions without sustained authority (Patent: 64/005,607)
- ADARA: Adversarial deception detection computing P(adversarial) from cross-sensor consistency and temporal anomalies
- ERAM: Escalation risk quantification for AI-enabled command-and-control decision compression
These are documented in four U.S. provisional patent submissions, seventeen DOI-registered Zenodo records (including research papers with full simulation data for the rover testbed, UAV platform, BLADE-EDGE defense platform, BLADE-AV automotive platform, BLADE-MARITIME maritime platform, and BLADE-INFRA critical infrastructure platform), and fifteen SSRN papers on AI governance and national security policy. Total: 33 published works with public DOIs and permalinks. The BLADE-SPACE orbital governance node (TRL 2-3 Preliminary Design, NASA SBIR EXPAND.3.S26B aligned) ships with a 15-document engineering package and is published on Zenodo (DOI 10.5281/zenodo.20183269).
Hardware Implementation. Twelve physical platforms demonstrating governance at increasing operational capability:
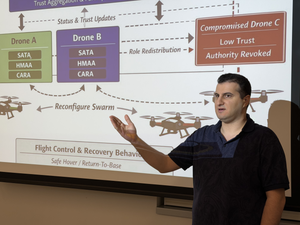
- Rover Testbed, 37 components, ~$484, SATA-HMAA-CARA pipeline, 350 simulation runs across 7 fault scenarios, TLA+ verified (48,751 states, 8 safety properties). DOI: 10.5281/zenodo.19143190.
- UAV Platform, 52 components, ~$4,200, MAVLink/HIL bridge for Cube Orange+ integration, 250 simulation runs across 5 adversarial scenarios, Monte Carlo campaign. DOI: 10.5281/zenodo.19128769.
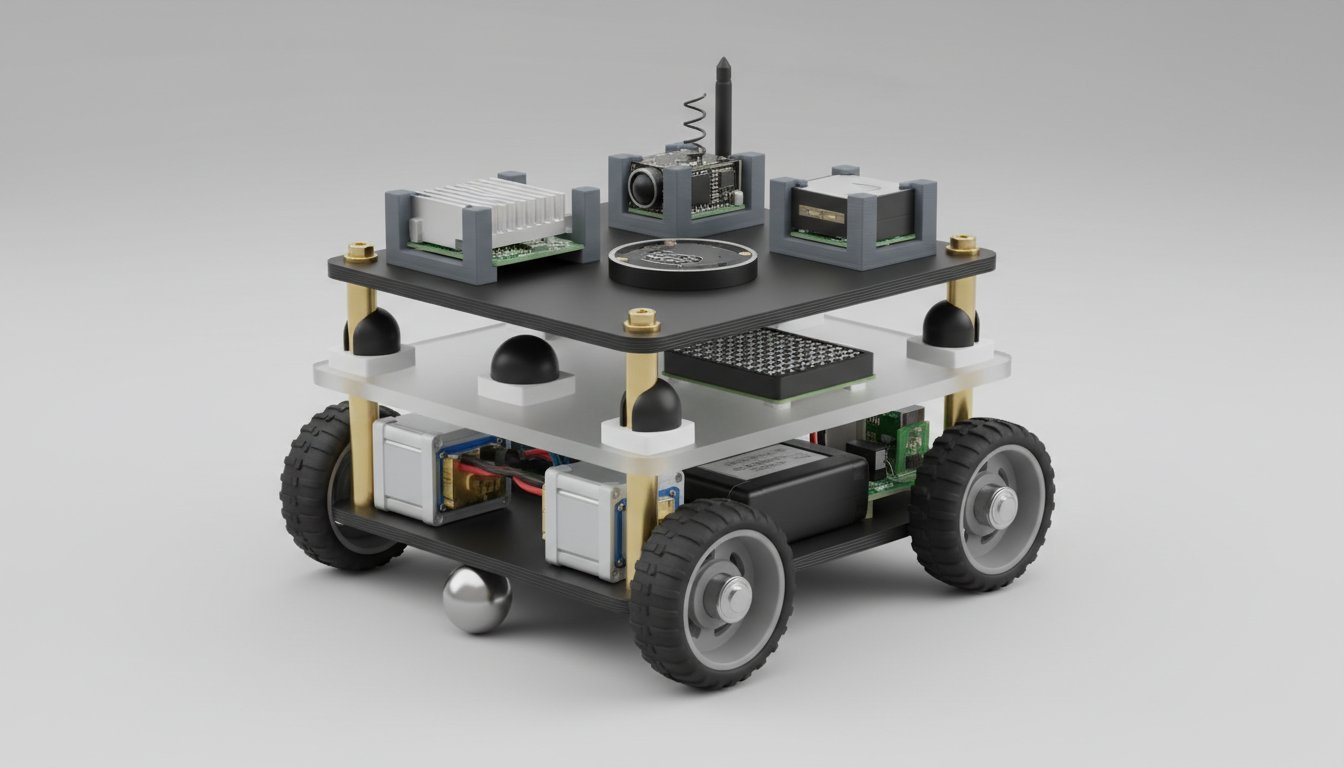
- BLADE-EDGE, 72 components, ~$139K, defense-grade directed-energy weapon governance. Dual Jetson AGX Orin + dual Zynq UltraScale+ FPGA. 9-module pipeline, MIL-STD-810G, hardwired safety interlock relay. DOI: 10.5281/zenodo.19177472.
- BLADE-AV, 62 components, ~$16K, autonomous vehicle drive-by-wire governance. 9-module pipeline, three-leg redundant KILOVAC LEV200 fail-safe relay. ISO 26262 ASIL-D, SAE J3016 L4. 1,200 runs, zero unsafe actions. DOI: 10.5281/zenodo.19232130.
- BLADE-MARITIME, 84 components, ~$43K, maritime surveillance governance. 9-module pipeline with hydroacoustic sonar, MAD, AIS spoofing detection, and sea-state authority damping. IP68 / MIL-STD-810G. DOI: 10.5281/zenodo.19246785.
- BLADE-INFRA, 92 components, ~$12K, critical infrastructure governance. 9-module pipeline with ICS/SCADA integration (IEC 61850, Modbus, PROFINET). SIL 3 / NERC CIP / FIPS 140-2. DOI: 10.5281/zenodo.19277887.
- BLADE-SPACE, 91 components, ~$505K, orbital governance node (TRL 2-3 Preliminary Design Phase). 9-stage pipeline on rad-tolerant compute (Microchip RTG4 FPGA + Aitech S-A1760 Venus SBC, hot-redundant); LEO 400-1200 km, 30 krad TID, 5-year design life; ECDSA P-256 audit chain; three-fault-tolerant safety interlock. 15-document engineering package. Aligned with NASA SBIR EXPAND.3.S26B. Zenodo DOI 10.5281/zenodo.20183269.
- BLADE-CUAS, counter-UAS authority governance node, ~$43.5K reference BOM (TRL 2-3 hardware / 3-4 simulation). 9-stage AUTHREX pipeline; four-tier HMAA (T3/T2/T1/T0) with federal-SLTT handoff; Dempster-Shafer consensus across radar, RF, EO/IR, Remote ID, LIDAR; ECDSA P-256 court-admissible evidence chain (Fed. R. Evid. 901/902/803(6)). Sixth BLADE platform, ~75% reuse from BLADE-EDGE. Aligned with EO 14305 and the FY26 NDAA Safer Skies Act. Zenodo DOI 10.5281/zenodo.20299604.
- BLADE-AGENT-HSM, agentic-AI hardware root of trust, ~$199 reference BOM (TRL 2-3 silicon / 3-4 emulator). Hardware companion to the AUTHREX-AGENT software shim; non-exportable ECDSA P-256/P-384 keys in a CC EAL6+ secure element; authority-tier state in a TPM 2.0 PCR bank; HKDF per-tool tokens; multi-modal tamper cascade. Five-opcode 64-byte ABI; USB-A stick and M.2 Key-E module. Seventh BLADE platform, first hardware root of trust. Aligned with CISA/NSA/Five Eyes agentic-AI guidance and FY26 NDAA Sections 1513 and 6601. Zenodo DOI 10.5281/zenodo.20299821.
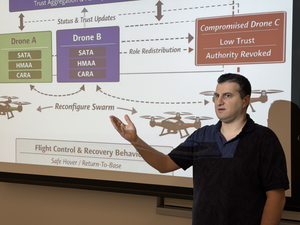
- BLADE-SWARM, attritable swarm authority governance, ~$1,333 per node reference BOM (TRL 3-4 simulator / spec, TRL 2 testbed). Byzantine-fault-tolerant two-phase consensus gated by SATA/HMAA/MAIVA across N=10/50/500 agents; tolerates f=(N-1)/3 compromised agents per quorum with a quorum-intersection bound; per-node ECDSA P-256 root of trust and hash-chained distributed audit ledger; TLA+ verified (5 safety, 3 liveness). Eighth BLADE platform; the multi-agent extension of the HMAA-UAV platform. Aligned with DoDD 3000.09, FY26 NDAA, and the NIST AI RMF. Zenodo DOI 10.5281/zenodo.20351198.
- BLADE-INFRA-OT, authority-governed IT/OT bridge for cross-boundary OT command adjudication, ~1U fanless reference design (TRL 2-3 hardware / 3-4 simulation). Fail-closed, bump-in-the-wire governance appliance at the IT/OT segmentation boundary; AUTHREX adjudicates each cross-boundary command to propagate, hold, or isolate across four OT authority regimes; Xilinx Kria K26 governance plane and x86 network plane; 48 BOM line items, 35 electrical, 42 mechanical; seed-deterministic SHA-256 tamper-evident audit ledger. Ninth BLADE platform; the operational-technology companion to BLADE-INFRA. Aligned with NIST SP 800-82, ISA/IEC 62443, and NERC CIP. Zenodo DOI 10.5281/zenodo.20342067.
- BLADE-FINANCE, authority governance for financial-sector AI decision systems under the U.S. Treasury Financial Services AI Risk Management Framework (TRL 3-4 simulation / TRL 2 hardware). Software-enforced authority-arbitration node; an eight-stage AUTHREX pipeline (VALIDATE through CARA) routes each transaction to autonomous clearance, supervised review, elevated confirmation, or manual hold; four-tier HMAA; a population-state coordination model across account, device, payee, and IP-cluster history; a retrospective stigmergic swarm-review module; SHA-256 canonical-form evidence chain; 36 components, 33 electrical, 32 mechanical, approximately $9,228 BOM. Tenth BLADE platform; first in the economic-security domain. Aligned with the U.S. Treasury FS AI RMF, NIST AI RMF, and EO 14179. Synthetic data only; not deployed in any financial institution. Zenodo DOI 10.5281/zenodo.20374692.
All ten BLADE platforms share the same governance pipeline architecture, demonstrating domain-agnostic portability across defense (DoDD 3000.09), automotive (ISO 26262), maritime (MIL-STD-810G), critical infrastructure (SIL 3 / NERC CIP), orbital (NASA EXPAND.3.S26B alignment), counter-UAS (EO 14305), and agentic AI (CISA/NSA/Five Eyes agentic-AI guidance). Combined across the four flight-relevant published platforms: 2,800+ experimental runs, zero unsafe actions. BLADE-SPACE is at TRL 2-3 (Preliminary Design); its V&V campaign is specified but not yet executed.
Software Implementation. A companion software authority-governance layer on the AUTHREX Systems venture site extends the same authority pipeline to additional settings, as six reference architectures (TRL 3-4, single-author research, not deployed): AUTHREX-AGENT (agentic AI), AUTHREX-ASSURE (pre-deployment assurance), AUTHREX-ICS-GATE (OT and critical infrastructure), AUTHREX-AGENT-CYBER (cyber-defense, governance only), AUTHREX-SPACECYBER (orbital autonomy), and AUTHREX-SANDBOX (test and evaluation). Several are software companions to the BLADE hardware platforms.
Simulation and Verification. Nineteen browser-based simulations with seeded PRNG for bit-exact reproducibility. G*Power justified sample sizes, Bonferroni correction, Shapiro-Wilk normality tests. All run client-side with zero dependencies, any reviewer can independently verify results.
Current Status. Independent Researcher based in Washington, DC, pursuing Georgetown University M.P.S. Applied Intelligence (STEM, in progress). B.Sc. Computer Science Engineering (USF, 3.45 GPA). MBA International Business (Lynn, 4.0 GPA). Governance architectures published on Zenodo under CC BY 4.0; ERAM published on SSRN. Next-phase: physical validation, TLA+/UPPAAL formal verification, ROS 2/Gazebo HIL testing, and ASIL-D certification pathway. This research program is informed by progressive professional experience across data governance, infrastructure security, and critical infrastructure systems, see Professional Background below, and sustained engagement with the defense, aerospace, and AI communities through industry conferences and professional societies.
Authority Lifecycle Governance
Assignment, delegation, monitoring, and revocation of operational authority in autonomous decision systems. Implemented in HMAA (U.S. Provisional 63/999,105). 42-file Python package, 98 tests, TLA+ verified (48,751 states). DOI: 10.5281/zenodo.18861653.
Fail-Safe Control Recovery
Deterministic recovery protocol for authority lockout events with GREP phased recovery and terminal non-compensatory policy gate. Implemented in CARA (U.S. Provisional 64/000,170). DOI: 10.5281/zenodo.18917790.
Decision Integrity Monitoring
Hardware-anchored sensor trust computation using weighted Dempster-Shafer fusion with cross-sensor validation and adversarial dynamics. Implemented in SATA (U.S. Provisional 64/002,453). DOI: 10.5281/zenodo.18936251.
Escalation Risk Assessment
Quantitative framework for decision-time compression and escalation pathway modeling in AI-enabled command-and-control systems. Documented in the ERAM framework. Published on SSRN.
Flash War Latency Control
FLAME: deterministic latency injection middleware preventing autonomous escalation in multi-domain command environments. 5-state Circuit Breaker State Machine, Dynamic Delay Function D(A, tier, domain). Patent: U.S. Provisional 64/005,607. DOI: 10.5281/zenodo.19015618.
Multi-Agent Trust Verification
MAIVA: Byzantine-resilient swarm trust aggregation with CUSUM-augmented detection, graduated escalation, and DoDD 3000.09 action gate classification. 37 self-tests, TLA+ specification. DOI: 10.5281/zenodo.19015517.
Adversarial Deception-Aware Risk
ADARA: proactive deception prior adjusting authority based on P(adversarial). Deception Probability Engine with Bayesian update and Phantom Fleet detection. DOI: 10.5281/zenodo.19043924.
UAV Governance Platform
HMAA-UAV: authority-governed flight autonomy for contested environments integrating SATA-HMAA-CARA into a 52-component UAV with Cube Orange+ and Jetson Orin NX. 250 simulation runs across 5 adversarial scenarios. DOI: 10.5281/zenodo.19128769.
Rover Testbed Platform
Authority-governed rover implementing the full 8-stage SATA-HMAA-CARA pipeline on a 37-component dual-compute platform (RPi5 + ESP32). 350 simulation runs, 7 fault scenarios, zero unsafe actions. DOI: 10.5281/zenodo.19143190.
BLADE-EDGE Governance Node
Defense-grade edge computing platform implementing all seven governance architectures on dual-redundant Jetson AGX Orin + Zynq UltraScale+ FPGA. 72 components, 103 connections, MIL-STD-810G rated. Hardware-enforced safety interlock. ~$139K prototype BOM. DOI: 10.5281/zenodo.19177472.
BLADE-AV Governance Node
Authority-governed drive-by-wire safety architecture for autonomous vehicles. 9-module pipeline on Jetson AGX Orin + Zynq UltraScale+. Three-leg redundant KILOVAC fail-safe. 62 components, 1,200 simulation runs, zero unsafe actions. ISO 26262 ASIL-D. ~$16K BOM. Cross-domain portability validated against BLADE-EDGE. DOI: 10.5281/zenodo.19232130.
BLADE-MARITIME Governance Node
Authority-governed maritime surveillance node with hydroacoustic sonar, magnetic anomaly detection (MAD), and AIS spoofing detection. Four maritime mathematical extensions: D-S fused trust, recursive AIS deception-risk, sea-state authority damping α(H), acoustic-delay-aware Byzantine consensus. 84 components, IP68 / MIL-STD-810G / MIL-STD-461G CE102. Third domain instantiation. $43K total BOM. DOI: 10.5281/zenodo.19246785.
BLADE-INFRA Governance Node
Authority-governed critical infrastructure protection node for ICS/SCADA systems, power grid monitoring, water treatment, and pipeline operations. IEC 61850 GOOSE, Modbus TCP/RTU, PROFINET IO. Pilz PNOZ S7.1 SIL-3 safety relay. 92 components, IP65, NERC CIP, FIPS 140-2 Level 3. Fourth domain instantiation. $11,590 BOM. DOI: 10.5281/zenodo.19277887.
BLADE-SPACE Governance Node
Authority-governed orbital governance node for autonomous LEO platforms beyond ground-loop latency. Microchip RTG4 FPGA + Aitech S-A1760 Venus SBC hot redundancy with <200 ms failover; ECDSA P-256 audit chain anchored in rad-tolerant TPM; three-fault-tolerant payload/thruster firing interlock; ADARA multi-constellation GNSS spoofing detection. 91 components, 6U+ SmallSat payload module, 30 krad TID, 5-year LEO mission life. Fifth domain instantiation (TRL 2-3 Preliminary Design Phase, NASA SBIR EXPAND.3.S26B aligned). $505,440 reference BOM. 15-document engineering package; Zenodo DOI 10.5281/zenodo.20183269.
BLADE-CUAS Governance Node
Authority-governed Counter-Unmanned Aircraft Systems (C-UAS) node for the post-EO 14305 multi-agency environment. Passive governance layer between commercial detection sensors and authorized operators; four-tier HMAA (T3/T2/T1/T0) federal-SLTT authority handoff; MAIVA Dempster-Shafer consensus across radar, RF, EO/IR, Remote ID, and LIDAR; ADARA Remote ID spoofing detection; ECDSA P-256 court-admissible evidence chain aligned with Fed. R. Evid. 901/902/803(6). Sixth domain instantiation (TRL 2-3 hardware / 3-4 simulation), approximately 75% architectural reuse from BLADE-EDGE. Aligned with EO 14305 and the FY26 NDAA Title LXXXVI Safer Skies Act. ~$43.5K reference BOM. DOI: 10.5281/zenodo.20299604.
BLADE-AGENT-HSM Hardware Root of Trust
Tamper-evident hardware root of trust for autonomous AI agents and the hardware companion to the AUTHREX-AGENT software shim. Signs the agent audit ledger with non-exportable ECDSA P-256/P-384 keys in an NXP EdgeLock SE051 (CC EAL6+) secure element; holds the four-tier HMAA authority state in an Infineon SLB 9670 TPM 2.0 (FIPS 140-2 Level 2) PCR bank; derives per-tool HKDF tokens; aggregates sub-agent spawn-quorum signatures; multi-modal tamper cascade (active PCB mesh, voltage-glitch, thermal) zeroizes keys and latches T0. Five-opcode 64-byte ABI; USB-A stick and M.2 Key-E module from one 4-layer PCB. Seventh BLADE platform and first hardware root of trust. Verified by an adversarial high-assurance emulator (275/275 deterministic checks, P-384 signed golden-trace anchor). Aligned with CISA/NSA/Five Eyes Careful Adoption of Agentic AI Services (1 May 2026) and FY26 NDAA Sections 1513 and 6601. ~$199 reference BOM. DOI: 10.5281/zenodo.20299821.
BLADE-SWARM Governance Node
Authority-governed coordination layer for attritable multi-agent swarms. Byzantine-fault-tolerant two-phase commit gated by SATA, HMAA, and MAIVA across N=10/50/500 agents, tolerating f=(N-1)/3 compromised agents per quorum with a quorum-intersection bound; per-node ECDSA P-256 root of trust and a hash-chained distributed audit ledger; TLA+ verified (5 safety, 3 liveness properties). Eighth BLADE platform; the multi-agent extension of the HMAA-UAV platform. Aligned with DoDD 3000.09, the FY26 NDAA, and the NIST AI RMF. ~$1,333 per-node reference BOM (TRL 3-4 simulator / spec, TRL 2 testbed). DOI: 10.5281/zenodo.20351198.
BLADE-INFRA-OT Governance Node
Authority-governed IT/OT bridge for cross-boundary OT command adjudication. Fail-closed, bump-in-the-wire governance appliance at the IT/OT segmentation boundary; AUTHREX adjudicates each cross-boundary command to propagate, hold for deliberation, or isolate across four OT authority regimes (NOMINAL, ELEVATED, LOCKDOWN, SAFE-HALT); malformed input fails closed. Xilinx Kria K26 governance plane and x86 network plane, managed Ethernet switch with SFP+ ports, ATECC608 root of trust, TPM 2.0, and a Form C fail-closed fault relay in a 1U fanless form factor; 48 BOM line items, 35 electrical, 42 mechanical connections; seed-deterministic SHA-256 tamper-evident audit ledger. Ninth BLADE platform; the operational-technology companion to BLADE-INFRA (TRL 2-3 hardware / 3-4 simulation). Aligned with NIST SP 800-82, ISA/IEC 62443, and NERC CIP. DOI: 10.5281/zenodo.20342067.
BLADE-FINANCE Governance Node
Authority governance for financial-sector AI decision systems under the U.S. Treasury Financial Services AI Risk Management Framework. A software-enforced authority-arbitration node placing a hardware-anchored checkpoint between automated transaction-decision models and consequential financial actions; an eight-stage AUTHREX pipeline routes each transaction to autonomous clearance, supervised review, elevated confirmation, or manual hold; four-tier HMAA; population-state coordination across account, device, payee, and IP-cluster history; a retrospective stigmergic swarm-review module recovers coordinated low-and-slow rings the per-transaction path clears; SHA-256 canonical-form evidence chain. Dual-plane compute (Xilinx Kria K26 governance, NVIDIA L4 inference) with a YubiHSM 2 in a FIPS 140-2 Level 3 enclosure; 36 components, approximately $9,228 BOM. Tenth BLADE platform; first in the economic-security domain (TRL 3-4 simulation / TRL 2 hardware). Aligned with the U.S. Treasury FS AI RMF, NIST AI RMF, and EO 14179. Synthetic data only. DOI: 10.5281/zenodo.20374692.
Software Authority-Governance Layer
Six software systems on the AUTHREX Systems venture site that carry the AUTHREX authority pipeline into agentic AI, OT and critical infrastructure, cyber-defense (governance only), orbital autonomy, and test and evaluation. Reference architectures (TRL 3-4), single-author research, not deployed.
Authority & Architecture Imprint
Three-trilogy / 10-volume technical reference series on autonomous-systems authority architecture: The Authority Equation (3 volumes), The Authority Discipline (4 volumes), and Autonomous Authority (3 volumes). Distributed via Amazon and IngramSpark in print and ebook formats. ISBNs registered through Bowker; The Authority Equation Volume I assigned Library of Congress Control Number 2026912260.
View Full Catalog at Authority & ArchitectureResearch Mission &
National Interest
This research addresses a critical technical gap: how authority is assigned, monitored, degraded, revoked, and recovered in autonomous systems where decisions occur faster than human reaction time. The proposed endeavor is evaluated under the Dhanasar three-prong framework for substantial merit, position to advance the work, and broader national benefit.
1. Substantial Merit & National Importance
Development of operational governance architectures for autonomous systems deployed in U.S. national security, defense, and critical infrastructure. Addresses priorities identified by DoD Directive 3000.09, DARPA Assured Autonomy, NIST AI RMF, NHTSA AV Framework, and the SELF DRIVE Act of 2026 (H.R. 7390). Cross-domain portability across defense (DoDD 3000.09), automotive (ISO 26262 ASIL-D), maritime (MIL-STD-810G), and critical infrastructure (SIL 3 / NERC CIP).
2. Well Positioned to Advance
This research produces substantial merit through peer-reviewable contributions: formal mathematical frameworks (weighted Dempster-Shafer sensor fusion, Byzantine fault-tolerant consensus, CUSUM anomaly detection), reproducible experimental protocols (seeded PRNG, 2,800+ experimental runs, zero unsafe actions), and open-access dissemination under MIT and CC BY 4.0 licenses.
Four U.S. provisional patents filed, 33 published works (18 Zenodo DOIs + 15 SSRN papers), seven governance architectures, twelve hardware research platforms, nineteen interactive simulations producing 2,800+ experimental runs with zero unsafe actions. Advanced degree: Georgetown University M.P.S. Applied Intelligence (STEM). B.Sc. Computer Science Engineering (USF). 140+ professional credentials including IEEE, AIAA, ACM, AAAI, INFORMS, NDIA, DARPAConnect, and Sigma Beta Delta Honor Society memberships. Active industry engagement across defense, aerospace, AI, and manufacturing trade shows and conferences.
3. Benefit to the United States
Fills gaps identified by Congress (H.R. 7390 cybersecurity requirements), NHTSA (1,429 AV incidents 2021-2025), and DoD (autonomous weapons governance). Supports defense modernization, automotive safety, maritime security, and critical infrastructure resilience. Prevents autonomous escalation (FLAME), detects adversarial manipulation (ADARA), and provides cryptographically auditable authority chains. Cross-domain portability demonstrated across four operational domains on one architectural foundation.
Includes Dhanasar analysis, research programs, future roadmap, policy impact, and deployment scenarios
Credentials & Background
Independently verifiable evidence of patents, publications, institutional affiliation, and professional experience. Every claim can be cross-checked through external systems: USPTO Patent Center, Zenodo, ORCID, Google Scholar, SSRN, ResearchGate, and employment records.
Verification Sources: Georgetown University M.P.S. Applied Intelligence (STEM) · Lynn University MBA (GPA 4.0) · USF B.Sc. Computer Science Engineering (STEM) · USPTO Patent Center · Zenodo · ORCID #0009-0001-8573-1667 · Google Scholar · SSRN · ResearchGate · Blue.Cloud · 7 professional roles 2017-Present.
Governance Architectures
for Autonomous Systems
Sensor Attestation & Trust Anchoring (SATA)
Hardware-anchored τ-Chain protocol producing continuous trust scalar τ ∈ [0,1] from TPM attestation records for autonomous mission authority.
Human-Machine Authority Architecture (HMAA)
Real-time authority computation engine with six-tier HMAS spectrum. Research platform: 42-file Python package with 98 tests, 7 validated experiments, TLA+ formal verification (48,751 states), Dempster-Shafer trust fusion, and deterministic simulation traces.
Adversarial Deception-Aware Risk Architecture (ADARA)
Proactive deception prior: A_adj = A_hmaa × (1 - λ × P_deception). Computes P(adversarial) from input anomalies, temporal correlation, cross-sensor consistency, and Bayesian mission history. Phantom Fleet detection module.
Multi-Agent Integrity Verification (MAIVA)
Byzantine-resilient swarm trust aggregation (3f+1 BFT), CUSUM-augmented detection, graduated escalation, DoDD 3000.09 action gates. 37 self-tests, TLA+ specification.
Flash War Latency Architecture (FLAME)
Strategic Latency as engineered system. Dynamic Delay Function D(A, tier, domain), 5-state Circuit Breaker with crypto-signed transitions, Keep-Alive heartbeat protocol.
Control Authority Regulation Architecture (CARA)
Deterministic authority recovery via GREP phases I-IV with non-compensatory terminal gate. 10M-iteration verification, 68-state control-flow enumeration.
Escalation Risk Assessment Model (ERAM)
Decision-time compression analysis for AI-enabled C2 systems. Quantitative framework modeling how authority integrity degrades across interconnected multi-domain environments.
Research Projects
Governance Architecture Projects
Seven governance architectures forming a unified authority lifecycle framework. Each is published with a DOI on Zenodo, implemented as an interactive simulation, and connected to twelve physical research platforms: Rover Testbed (~$484), UAV Platform (~$4,200), BLADE-EDGE (~$139K), BLADE-AV (~$16K), BLADE-MARITIME (~$43K), BLADE-INFRA (~$12K), BLADE-SPACE (~$505K, TRL 2-3 Preliminary Design), BLADE-CUAS (~$43.5K, counter-UAS, TRL 2-3), BLADE-AGENT-HSM (~$199, agentic-AI hardware root of trust, TRL 2-3 silicon / 3-4 emulator), BLADE-SWARM (~$1,333/node, attritable swarm autonomy, TRL 3-4 simulator / spec), BLADE-INFRA-OT (~1U fanless, IT/OT bridge governance, TRL 2-3 hardware / 3-4 simulation), and BLADE-FINANCE (~$9,228, financial-sector AI governance, TRL 3-4 simulation / 2 hardware).
Real-time authority computation engine. Four-level state machine (A3-A0) with hysteresis transitions. TLA+ verified: 48,751 states, 8 properties, 98 tests.
View Project DetailsDeterministic recovery for authority lockout. Four-phase GREP pipeline (Guard, Reduce, Evaluate, Promote) with terminal non-compensatory policy gate.
View Project DetailsFoundation trust layer using weighted Dempster-Shafer belief functions. Four diagnostics: internal consistency, cross-sensor agreement, temporal stability, physical plausibility.
View Project DetailsStrategic Latency as a formal system. 5-state Circuit Breaker with Dynamic Delay Function D(A, tier, domain) preventing autonomous escalation in multi-domain command.
View Project DetailsByzantine-resilient swarm trust aggregation. Trimmed weighted median resistant to f adversaries in 3f+1 rosters, CUSUM anomaly detection, DoDD 3000.09 action gates.
View Project DetailsProactive deception prior adjusting authority via P(adversarial). Deception Probability Engine with Bayesian update. Phantom Fleet detection for AI-hallucinated hostile scenarios.
View Project DetailsEscalation risk quantification across interconnected autonomous command nodes. Models how autonomous actions cascade across domain boundaries. 6 scenarios, 600 Monte Carlo runs.
View Project DetailsSoftware Research Platforms
The software authority-governance layer that the hardware platforms anchor in silicon. Published and maintained on the AUTHREX Systems venture site, where each system has a full technical page with scenarios, standards mapping, and a reference design.
Software authority-lifecycle shim for autonomous AI agents: four-tier HMAA authority gating, per-tool HKDF authorization, spawn quorum, and a hash-chained audit ledger, anchored in hardware by the BLADE-AGENT-HSM root of trust. Designed to contain indirect prompt-injection attacks against tool-using agents. Single-author research, not deployed.
View on AUTHREX SystemsPre-deployment authority governance for autonomous systems: assurance gating that must clear before a system is permitted to act. Reference architecture aligned with the 2026 National Cybersecurity Strategy and NDAA Section 1533. Single-author research, not deployed.
View on AUTHREX SystemsOperational-technology authority governance for critical infrastructure, gating AI actions across the IT/OT boundary. Aligned with CISA/NSA AI-in-OT principles, NIST SP 800-82, ISA/IEC 62443, and NERC CIP. Single-author research, not deployed.
View on AUTHREX SystemsAuthority governance for autonomous cyber-defense agents, constraining what a defensive AI may do and when. Governance only, with no offensive function. Aligned with Five Eyes Careful Adoption of Agentic AI Services, DARPA AIxCC, and NDAA Section 1513.
View on AUTHREX SystemsOnboard authority governance for orbital autonomy, gating autonomous spacecraft actions under intermittent ground contact. Aligned with NASA SBIR 2026 BAA subtopic EXPAND.3.S26B and Space Policy Directive 5. Single-author research, not deployed.
View on AUTHREX SystemsTest-and-evaluation authority governance: governs what an AI under evaluation is permitted to do inside the sandbox. Aligned with NDAA Section 1534 and Section 1533. Single-author research, not deployed.
View on AUTHREX SystemsHardware Research Platforms
Twelve physical platforms implementing the governance architectures at increasing levels of operational capability. Each is published as a complete reproducible artifact package with full hardware specifications, simulation data, and assembly documentation.
A low-cost experimental platform for studying authority-governed autonomy in safety-critical robotic systems under contested conditions. The rover continuously evaluates how much it can trust each of its sensors, computes how much authority the autonomy software should have right now, and falls back to a safe state when trust collapses. All in a dual-compute architecture (Raspberry Pi 5 + ESP32). 37 verified components, 76 electrical connections, 7 defined experiments. Platform cost under $500.
View Project Details
A trust-governed autonomous drone where every flight decision is evaluated by sensor trust fusion (SATA), authority governance (HMAA), and recovery logic (CARA). Cube Orange+ flight controller with NVIDIA Jetson Orin NX AI companion computer. 52 verified components, 48 electrical connections, 49 mechanical assemblies. Carbon fiber quadcopter frame.
View Project Details
Authority governance for attritable autonomous swarms at N=10 (physical testbed), N=50 (combined operation), and N=500 (DAWG-class). Each agent runs a Byzantine-fault-tolerant two-phase consensus gated by SATA peer trust, the four-tier HMAA authority state, and weighted MAIVA voting before the swarm commits, tolerating up to f=(N-1)/3 compromised agents per quorum with a quorum-intersection bound and safe-halt-by-default under denied or degraded RF. Per-node ECDSA P-256 root of trust (ATECC608B) feeds a hash-chained distributed audit ledger. TLA+ verified (5 safety + 3 liveness); ~$1,333 per node. It governs decision authority and audit; it does not govern weapons. Eighth domain: defense, automotive, maritime, critical infrastructure, orbital, counter-UAS, agentic AI, swarm autonomy.
View Project Details
A rugged, portable edge computing device serving as the ethical decision-making authority for autonomous defense platforms. Implements the complete 9-module governance pipeline (SATA → ADARA → IFF → HMAA → MAIVA → FLAME → CARA → BDA → EFFECTOR) on dual-redundant Jetson AGX Orin + Zynq UltraScale+ hardware. 72 components, 103 connections, MIL-STD-810G rated. Hardware-enforced safety interlock (normally-open relay). ~$139K prototype BOM.
View Project Details
Authority-governed drive-by-wire safety architecture for autonomous vehicles. 9-module governance pipeline on Jetson AGX Orin + Zynq UltraScale+. Three-leg redundant KILOVAC fail-safe relay. 62 components, 1,200 simulation runs, zero unsafe actions. ~$16,287 BOM. Cross-domain portability validated against BLADE-EDGE defense variant.
View Project Details
Authority-governed maritime surveillance node with hydroacoustic sonar, magnetic anomaly detection (MAD), and AIS spoofing detection. Four maritime mathematical extensions to the BLADE governance pipeline. 84 components, IP68 enclosure, MIL-STD-461G CE102 power chain. Third domain instantiation: defense → automotive → maritime.
View Project Details
Authority-governed critical infrastructure protection node for ICS/SCADA systems, power grid monitoring, and industrial process control. IEC 61850 GOOSE, Modbus TCP/RTU, PROFINET IO integration. Pilz PNOZ S7.1 SIL-3 safety relay. 92 components, IP65 DIN-rail enclosure. Fourth domain instantiation: defense → automotive → maritime → critical infrastructure.
View Project Details
A fail-closed, bump-in-the-wire governance appliance at the segmentation boundary between corporate IT networks and operational-technology control assets. Each cross-boundary command is parsed, scored, and adjudicated through the AUTHREX pipeline to one of three actions: propagate, hold for deliberation, or isolate. Four OT authority regimes; malformed input fails closed. Xilinx Kria K26 governance plane and x86 network plane, managed Ethernet switch with SFP+ ports, ATECC608 root of trust, TPM 2.0 measured boot, and a Form C fail-closed fault relay in a 1U fanless form factor (48 BOM line items). Every decision is written to a seed-deterministic SHA-256 hash-chained audit ledger. Ninth domain: the IT/OT boundary (operational technology), companion to BLADE-INFRA.
View Project Details
Authority-governed orbital governance node for autonomous LEO platforms beyond ground-loop latency. Microchip RTG4 FPGA + Aitech S-A1760 Venus SBC hot redundancy with <200 ms failover; ECDSA P-256 audit chain anchored in rad-tolerant TPM; three-fault-tolerant payload/thruster firing interlock. 91 components, 6U+ SmallSat payload module, 30 krad TID, 5-year LEO mission life. Fifth domain instantiation: defense → automotive → maritime → critical infrastructure → orbital.
View Project Details
Authority-governed Counter-Unmanned Aircraft Systems (C-UAS) node for the post-EO 14305 multi-agency environment. Passive governance layer between commercial detection sensors and authorized operators; four-tier HMAA (T3/T2/T1/T0) with federal-SLTT handoff; Dempster-Shafer multi-modal consensus through MAIVA; ECDSA P-256 court-admissible evidence chain aligned with Fed. R. Evid. 901/902/803(6). ~75% architectural reuse from BLADE-EDGE; ~$43.5K reference BOM. Sixth domain: defense, automotive, maritime, critical infrastructure, orbital, counter-UAS.
View Project Details
Tamper-evident hardware root of trust for autonomous AI agents and the hardware companion to the AUTHREX-AGENT software shim. Signs the agent audit ledger with non-exportable ECDSA P-256/P-384 keys in a CC EAL6+ secure element; holds the four-tier HMAA authority state in a TPM 2.0 PCR bank; derives per-tool HKDF tokens; multi-modal tamper cascade zeroizes keys and latches T0. Five-opcode 64-byte ABI; USB-A stick and M.2 Key-E module; ~$199 reference BOM. Verified by an adversarial high-assurance emulator (275/275 deterministic checks). Seventh domain: defense, automotive, maritime, critical infrastructure, orbital, counter-UAS, agentic AI.
View Project Details
A hardware-anchored authority layer between automated transaction-decision models and consequential financial actions. Every transaction is scored through the eight-stage AUTHREX pipeline and routed to one of four authority tiers: autonomous clearance, supervised review, elevated confirmation, or manual hold. A retrospective stigmergic swarm-review module recovers coordinated low-and-slow rings the per-transaction path clears. Aligned to the U.S. Treasury Financial Services AI RMF. First BLADE platform in the economic-security domain. Synthetic data only; not deployed in any financial institution.
View Project DetailsInteractive Technical
Demonstrations
Each simulation is a fully functional, browser-based implementation of the corresponding architecture or technical report. These are not mockups: they execute the actual algorithms described in the filed patent disclosures and published specifications, with real-time computation, cryptographic operations, and verifiable outputs.
Coverage: Seven governance architectures (SATA, HMAA, CARA, MAIVA, FLAME, ADARA, ERAM), four BLADE hardware reference platforms (EDGE, AV, MARITIME, INFRA), and two physical testbeds (Rover UGV, UAV). All simulations are browser-based JavaScript implementations of the published algorithms, accessible without registration or installation.
Problem, Solution, Impact
All architectures presented in this work are components of a unified authority-governed autonomy framework. SATA evaluates system trust, HMAA computes authority constraints, CARA enforces recovery behavior, MAIVA governs multi-agent participation, FLAME regulates decision timing, ADARA detects adversarial deception, and ERAM quantifies escalation risk in command-and-control environments. Together, these components form a structured approach to controlling autonomous systems under uncertainty. The BLADE-EDGE Governance Node implements all seven architectures in a single defense-grade device, and the BLADE-AV Governance Node demonstrates automotive portability under ISO 26262, and the BLADE-MARITIME Governance Node extends the pipeline to maritime surveillance under MIL-STD-810G, and the BLADE-INFRA Governance Node extends it to critical infrastructure protection under SIL 3 / NERC CIP, and the BLADE-SPACE Governance Node extends it to the orbital domain (TRL 2-3 Preliminary Design Phase) with radiation-tolerant compute and ECDSA-anchored audit, aligned with NASA SBIR EXPAND. The BLADE-CUAS Governance Node extends it to the counter-UAS domain, arbitrating federal-SLTT authority for Counter-Unmanned Aircraft Systems operations under EO 14305 and the FY26 NDAA Safer Skies Act. The BLADE-AGENT-HSM extracts the trust anchor into a standalone tamper-evident device, the hardware companion to the AUTHREX-AGENT software shim, extending the same hardware-rooted authority and audit chain to autonomous AI agents under the CISA/NSA/Five Eyes agentic-AI guidance and FY26 NDAA Sections 1513 and 6601. The BLADE-SWARM Governance Node extends the pipeline to coordinated multi-agent swarms, gating every swarm commit on Byzantine-fault-tolerant sub-quorum consensus (SATA, HMAA, MAIVA) across N=10/50/500 attritable agents with a hash-chained distributed audit ledger, aligned with DoDD 3000.09 and the FY26 NDAA. The BLADE-INFRA-OT Governance Node extends the pipeline to the IT/OT boundary, adjudicating each cross-boundary command at the segmentation seam between corporate IT networks and operational-technology control assets, failing closed on malformed input, aligned with NIST SP 800-82, ISA/IEC 62443, and NERC CIP.
Future Research Directions
Exploratory directions under consideration. Neither has been built, simulated, or published, and neither is part of the current portfolio.
The AUTHREX authority-governance model is designed to generalize across safety-critical domains beyond those already instantiated. Two public-interest directions are under consideration:
Medical-device AI governance (working name BLADE-MED-DEVICE). Applying authority arbitration to AI/ML-enabled medical devices, framed against the U.S. FDA Software-as-a-Medical-Device Action Plan and Predetermined Change Control Plan (PCCP) pathway, FDA premarket cybersecurity guidance, IEC 62304, and ISO 13485.
Rail autonomous-control authority (working name BLADE-RAIL). Extending the model to rail and transit control, framed against FRA Positive Train Control, CBTC standards (IEEE 1474, IEC 62290), and the Transportation Systems critical-infrastructure sector.
Research Papers
& Policy Analysis
33 DOI-registered research works across Zenodo and SSRN covering autonomous systems governance, AI defense doctrine, escalation risk, authority lifecycle architecture, and quantum-communications governance. All publications are open-access and verifiable via DOI or SSRN abstract IDs.
Distribution: 15 SSRN scholarly papers (Author Rank 15,210 of 2,727,789, top 0.56%), 18 Zenodo DOI deposits (Georgetown University institutional affiliation). Topics span autonomous systems governance, AI defense doctrine, escalation risk in AI-enabled military command and control, authority lifecycle governance, autonomous space operations, quantum-communications governance, and counter-tunnel architectures.
AUTHREX Systems
AUTHREX Systems is a research initiative demonstrating authority lifecycle governance infrastructure for autonomous systems. It integrates the seven governance frameworks, ten BLADE hardware platforms, and nineteen validated simulations developed through this research program into a single unified platform, providing end-to-end authority control across defense, maritime, infrastructure, and autonomous vehicle domains.
Standards Alignment: DoDD 3000.09 (Autonomy in Weapon Systems), NIST AI RMF 1.0 (AI Risk Management), MIL-STD-882E (System Safety), ISO 26262 ASIL-D (Automotive), IEC 61508 SIL 3 (Industrial), NERC CIP (Energy Grid), FIPS 140-2 Level 3 (Cryptographic).
Technology Readiness, Terminology
& Dual-Use Mapping
Three companion technical reference artifacts: Technology Readiness Level classification across 14 governance components and hardware platforms; AUTHREX terminology mapped to standard academic and industry equivalents; and a defense-to-civilian dual-use application matrix demonstrating cross-domain portability.
TRL Progression Target: Current portfolio spans TRL 3-4 (proof of concept through lab validation). FPGA governance bitstream commissioning (Q3 2026) and physical testbed flight validation (Q4 2026) target TRL 5-6. SBIR Phase II proposal planned for Q4 2026.
Technical Credentials
& Domain Expertise
- IEEE Member (#102193505)
- AIAA Student Member (#1936005)
- ACM Member (#9952787)
- AAAI Member (#656504)
- INFORMS Member (#2009712)
- NDIA Member (#1700222)
- Sigma Beta Delta Honor Society, Lifetime Member (#2007930)
- CompTIA Security+
- CISSP Domain 1: Security & Risk Management
- NIST Risk Management Framework (RMF)
- NIST 800-171 Awareness
- NIST Cybersecurity Framework (CSF)
- AI Strategy (Oxford / Wharton Executive Education)
- AI in National Security (SCSP)
- Generative AI Governance (University of Michigan)
- Open-Source Intelligence (Basel Institute on Governance)
- Advanced System Security Design (University of Colorado)
- AI for Cybersecurity (Johns Hopkins University)
- NYU Cybersecurity Specialization
- Cloud Computing Security (University of Colorado)
Conferences, Forums & Professional Development
Active participation in defense, aerospace, AI, and autonomous systems communities through trade shows, technical conferences, professional society events, and continuing education. Sustained engagement across these communities ensures that AUTHREX governance architectures remain aligned with operational requirements, emerging standards, and the evolving needs of the U.S. defense and critical infrastructure sectors.
-
DARPAConnect Mission Connect - Defense Advanced Research Projects Agency · Ann Arbor, MI
May 7, 2026 · DARPA regional outreach event for researchers, innovators, and small-business performers -
NHTSA Automated Vehicle Safety Public Comment - National Highway Traffic Safety Administration · regulations.gov
Apr 27, 2026 · Technical public comment submitted to NHTSA Docket NHTSA-2026-0265 (Automated Vehicle Safety Public Meeting) proposing AUTHREX trust-proportional authority governance for ADS sensor-degradation scenarios · Comment ID NHTSA-2026-0265-0014 ↗ -
Defense Technology Alliance Roundtable at Israel Tech Week Miami 2026 · Washington, DC
2026 · U.S.-Israel defense technology cooperation, autonomous systems, AI, cybersecurity -
SHOT Show 2026 - NSSF · Las Vegas, NV
Jan 20-23, 2026 · Defense, law enforcement, tactical technology -
NBAA Regional Forum 2026 - National Business Aviation Association · Opa-locka, FL
Feb 25, 2026 · Business aviation, 3,000+ attendees, 200+ exhibitors, aircraft display -
NBAA Regional Forum 2025 - National Business Aviation Association · Orlando, FL
Feb 26, 2025 · Business aviation, aircraft display, 100+ exhibitors -
Israel Tech Week 2025 · Washington, DC
2025 · Israeli tech innovation, defense-tech, AI, cybersecurity -
Miami AI Hub - Meetup Community · Washington, DC
Multiple sessions 2024-2026 · AI applications, networking, industry talks -
SupplySide West & Fi North America 2025 - Informa · Las Vegas, NV
Oct 27-30, 2025 · Supply chain, industrial technology, 20,000+ professionals -
SHOT Show 2024 - NSSF · Las Vegas, NV
Jan 23-26, 2024 · Defense industry, firearms, law enforcement technology -
NBAA Regional Forum 2024 - National Business Aviation Association · Opa-locka, FL
2024 · Business aviation, aircraft display, aerospace technology -
EMO Hannover 2023 - Deutsche Messe · Hannover, Germany
Sep 18-23, 2023 · World's leading metalworking & manufacturing technology trade fair
-
Registration Confirmed
NDIA 2026 Emerging Technologies for Defense Conference & Exhibition · Washington, D.C.
September 9-10, 2026 · AI, autonomous systems, cyber, next-gen defense technologyAbstract Submitted "Trust-Proportional Authority Governance for Autonomous Defense Systems: Bridging the Runtime Governance Gap": Technical Presentation & Poster · Game-Changing Emerging Technologies track · Submission ID 2421887 -
Abstract Submitted
AIAA SciTech Forum 2027 · Orlando, FL
January 11-15, 2027 · Aerospace technology, autonomy, certification"Trust-Proportional Authority Governance for Uncrewed Autonomous Systems: Formally Verified Runtime Authority Management": Technical Paper · Uncrewed and Autonomous Systems: Certification Concepts for Increasingly Autonomous Systems track · Control ID 4555075 · Notification expected on or about August 24, 2026 -
Abstract Submitted
SpaceCom 2027
2027 · Commercial space, autonomous space systems, governance"Trust-Proportional Authority: Solving the Governance Gap for Autonomous Space Systems", Speaker submission -
AAAI Summer Symposium Series 2026, Burlingame, CA
May 19-21, 2026 · Safe AI, autonomous systems safety, multi-agent teamwork -
AUVSI XPONENTIAL 2026, Detroit, MI
May 11-14, 2026 · Autonomous systems, UAS, NDIA/MDEX defense theater -
AIAA AVIATION Forum 2026
May 19-21, 2026 · Aerospace systems, autonomy, defense innovation -
NDIA Future Force Capabilities (FFC) 2026
2026 · Robotics, autonomous systems, munitions technology -
NBAA-BACE 2026 - National Business Aviation Association · Las Vegas, NV
Oct 20-22, 2026 · World's largest business aviation convention & exhibition -
SHOT Show 2027 - NSSF · Las Vegas, NV
Jan 19-22, 2027 · Defense and tactical technology trade show
-
AIAA: The Anatomy of Autonomy
Online Short Course · Technology, integration & applications across aviation & space -
AIAA: Generative AI for Code Generation
Online Short Course · AI-driven engineering and evaluation methods -
AIAA: Flight Test Techniques for UAS
Online Short Course · Development, qualification, and acceptance tests -
AAAI-26 Conference Content
On-demand access via Underline.io · AI research presentations and workshops
-
IEEE, Webinars, technical publications, standards development
Member #102193505 · Autonomous systems, safety-critical engineering -
AIAA, Forums, short courses, student conferences
Member #1936005 · Aerospace, defense, uncrewed systems -
ACM, TechTalks, digital library, computing research
Member #9952787 · AI governance, formal verification, algorithms -
AAAI, Conference content, symposia, AI safety research
Member #656504 · Artificial intelligence, multi-agent systems -
INFORMS, Analytics, operations research, decision science
Member #2009712 · Monte Carlo methods, decision-making under uncertainty -
NDIA, Defense conferences, emerging tech, acquisition
Member #1700222 · Defense industry, autonomous systems, cyber
Impact & Recognition
Independent third-party citations, academic references, and professional community recognition of AUTHREX governance research, generated without solicitation by university journals, defense communities, and academic platforms across multiple countries.
A public comment by Burak Oktenli (Docket NHTSA-2026-0529-0007) is cited by name in the U.S. Federal Register: NHTSA, Incident Reporting for Automated Driving Systems (ADS) and Level 2 ADAS, 91 FR 30789 (May 26, 2026), among public comments referenced in the notice, which also include submissions from Virginia DOT, the Alliance for Automotive Innovation, and Consumer Reports. Verify on federalregister.gov.
Citing Sources: Joey Hernandez / Pomona College Department of Economics (The Cascade Protocol book, ISBN 979-8195946579, May 2026), University of Toronto LexAI Journal (ERAM framework, Ref #4), Jorge Enrique Rivera Rojas / Colombia (defense logistics, cited alongside DoD & USDA), SSRN Community / Elsevier (submarine signatures), Wargaming Weekly / Bluesky (AI-driven simulation), Haberler.com / Turkey (media feature).
Research & Publication Presence
ORCID
0009-0001-8573-1667, Verified researcher identity with Georgetown University affiliation
Google Scholar
Full publication index with citations and research metrics
SSRN
Policy and strategic research papers on AI governance, escalation risk, and national security
ResearchGate
Research profile with publications, metrics, and academic networking
Zenodo
14 DOI-registered research artifacts with Georgetown University affiliation (CC BY 4.0)
OpenReview
Open peer review platform for AI and machine learning research
GitHub
Source code repositories for AUTHREX governance architectures and research platforms
GitLab
Mirror repositories and CI/CD pipelines for governance architecture research
Professional network profile with career history and research connections
Get In Touch
Available for research collaborations, expert advisory engagements, and discussions on AI governance, autonomous systems safety, and national security technology policy.
Washington, DC
English (Professional) · Turkish (Native) · Russian (Reading Proficiency)
AI Governance · Autonomous Systems Safety · National Security Technology · Escalation Risk Modeling · Human-Machine Teaming
HMAA: U.S. Provisional 63/999,105 (March 7, 2026) · CARA: U.S. Provisional 64/000,170 (March 9, 2026) · SATA: U.S. Provisional 64/002,453 (March 11, 2026) · FLAME: U.S. Provisional 64/005,607 (March 14, 2026) · All submitted via USPTO Patent Center, awaiting review