BLADE-AV Governance Node
BLADE-AV = Authority-Governed Drive-by-Wire Safety Architecture for Autonomous Vehicles
A hardware-enforced authority gating system for autonomous vehicle drive-by-wire control. Integrates Dempster-Shafer trust fusion, four-level authority with hysteresis, Byzantine fault-tolerant consensus, deliberation windows, and deterministic recovery, all enforced through a three-leg redundant fail-safe circuit driving a normally-open KILOVAC LEV200 safety relay.
Published on Zenodo · DOI: 10.5281/zenodo.19232130This is the second domain instantiation of the BLADE governance pipeline, after BLADE-EDGE (defense), demonstrating that authority-governed autonomy is domain-agnostic. The same governance pipeline applies directly to civilian autonomous vehicles under ISO 26262 ASIL-D, SAE J3016, and NHTSA ADS requirements.
Key Contributions
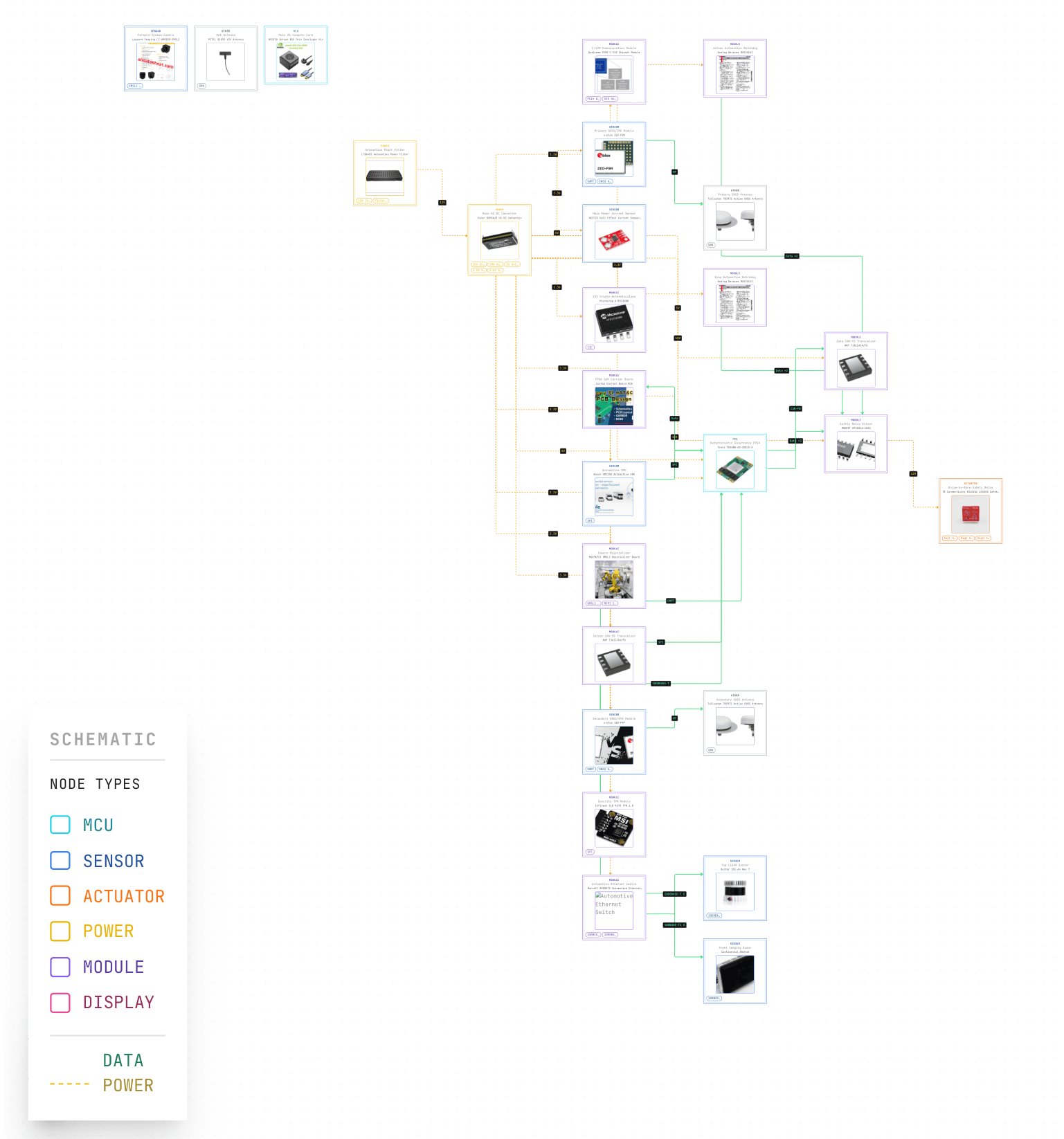
- 9-module authority-governed pipeline: SATA → ADARA → IFF → HMAA → MAIVA → FLAME → CARA → BDA → EFFECTOR
- Formal Dempster-Shafer trust fusion with binary frame Θ = {Trusted, Untrusted} and per-sensor BPA construction
- Three-leg redundant fail-safe: Zynq GPIO + Zynq MAX16161 watchdog + Jetson MAX16161 watchdog → BTS5016-1EKD → KILOVAC LEV200
- Dual-compute: NVIDIA Jetson AGX Orin 64GB (AI/perception) + Trenz TE0808 Zynq UltraScale+ (FPGA governance)
- Zero unsafe actions across 1,200 simulation runs (100 per scenario × 12 attack vectors)
- ISO 26262 ASIL-D target architecture with automotive-grade components (AEC-Q100)
- Cross-domain portability validated against BLADE-EDGE defense variant
Zenodo Publication: Oktenli, B. (2026). BLADE-AV Governance Node: Authority-Governed Drive-by-Wire Safety Architecture for Autonomous Vehicles (v1.0). Zenodo. https://doi.org/10.5281/zenodo.19232130