BLADE-MARITIME Governance Node
BLADE-MARITIME = Authority-Governed ASV Governance Node for Maritime Surveillance
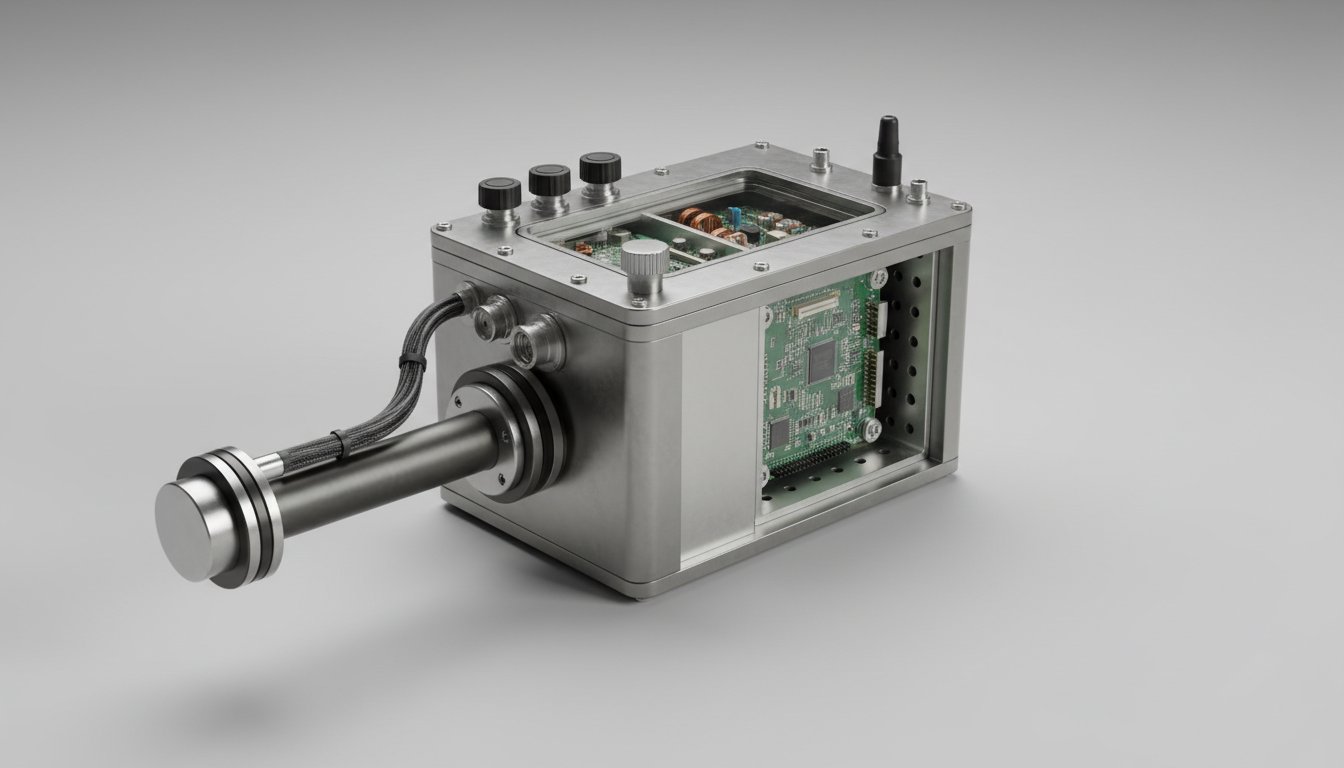
A hardware-enforced authority gating system for maritime autonomous surface vehicle control. Integrates Dempster-Shafer trust fusion, four-level authority with hysteresis, Byzantine fault-tolerant consensus, deliberation windows, and deterministic recovery, all enforced through a dual-GPIO safety interlock circuit driving a normally-open SPDT 24VDC safety relay.
Published on Zenodo · DOI: 10.5281/zenodo.19246785This is the third domain instantiation of the BLADE governance pipeline, after BLADE-EDGE (defense) and BLADE-AV (automotive), extending authority-governed autonomy to maritime autonomous surface vehicles under MIL-STD-810G / IP68, MIL-STD-461G CE102, and DoDD 3000.09.
Key Contributions
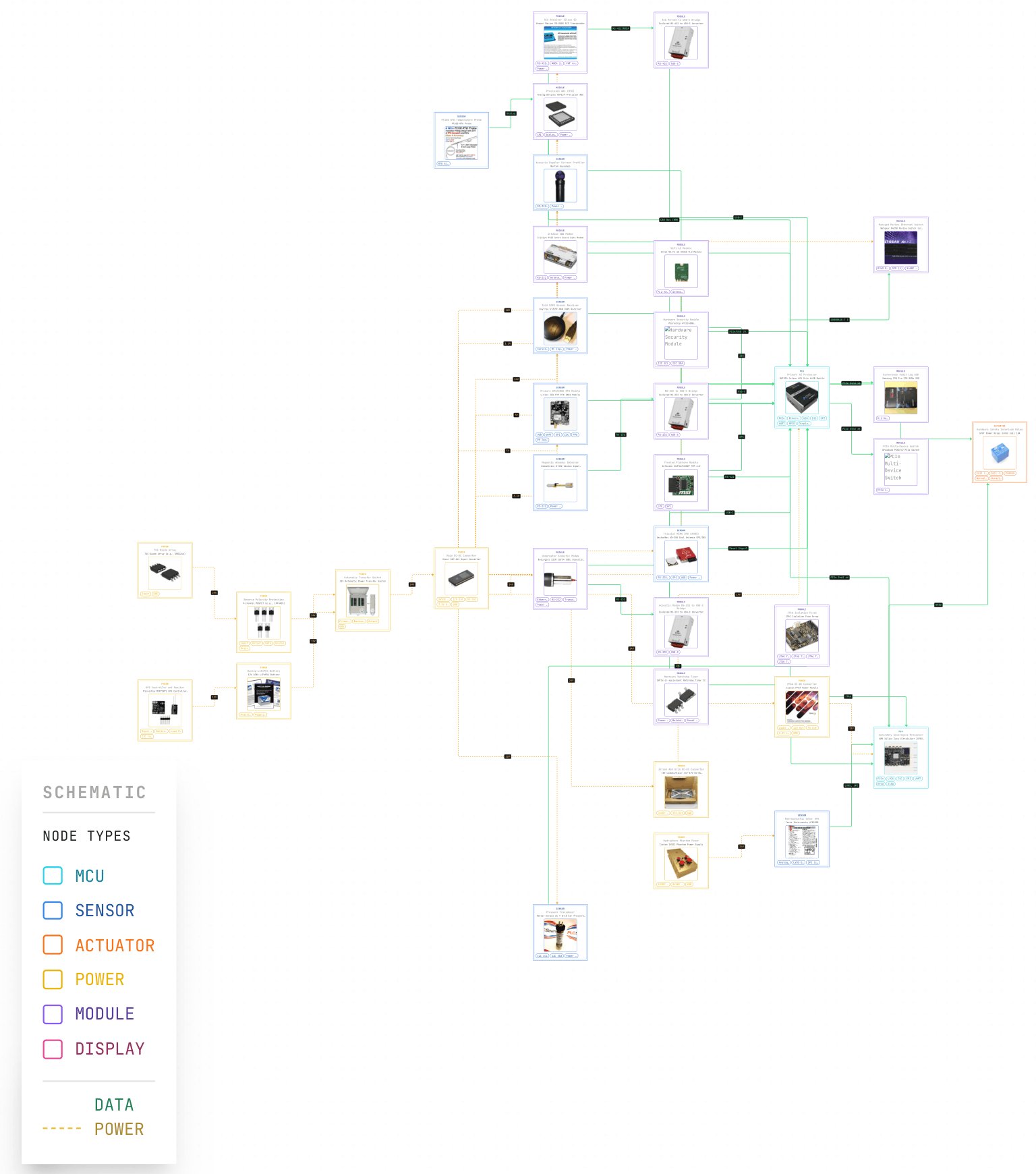
- 9-module authority-governed pipeline: SATA → ADARA → IFF → HMAA → MAIVA → FLAME → CARA → BDA → EFFECTOR
- Formal Dempster-Shafer trust fusion with binary frame Θ = {threat, non-threat} with hydroacoustic + MAD per-sensor mass functions
- Dual-GPIO hardware safety interlock: Zynq PASS + Jetson APPROVE + TPS3823 watchdog (500ms timeout) → normally-open SPDT relay (24VDC coil)
- Dual-compute: NVIDIA Jetson AGX Orin 64GB (AI/perception) + Zynq UltraScale+ ZU7EV (FPGA governance)
- Thirteen fault injection scenarios with multi-select compose in browser simulation (v3.11, 4,897 lines)
- IP68 / MIL-STD-810G / MIL-STD-461G CE102 target architecture with MIL-spec power chain (300W Vicor DCM5614, 32% margin)
- Cross-domain portability validated against BLADE-EDGE defense variant
Zenodo Publication: Oktenli, B. (2026). BLADE-MARITIME Governance Node: Authority-Governed Maritime Surveillance Node with Hydroacoustic, Magnetic Anomaly Detection, and Multi-Modal Sensor Fusion (v2.3). Zenodo. https://doi.org/10.5281/zenodo.19246785