BLADE-EDGE Governance Node
BLADE-EDGE = Beam-Layer Authority for Directed Engagements, Edge Node
A rugged, portable edge computing device that serves as the ethical decision-making authority for autonomous defense platforms, determining in real-time whether systems should EXECUTE, DELAY, ABORT, or HANDOFF based on multi-sensor trust consensus.
Design Complete · Published on Zenodo · DOI: 10.5281/zenodo.19177472This is NOT a weapon. It is a governance layer, a hardware-enforced ethical checkpoint that sits between autonomous defense systems and lethal action. It implements the human-judgment requirements mandated by DoD Directive 3000.09 directly in silicon and firmware.
Key Contributions
- Hardware-enforced ethical checkpoint implementing DoDD 3000.09 in silicon
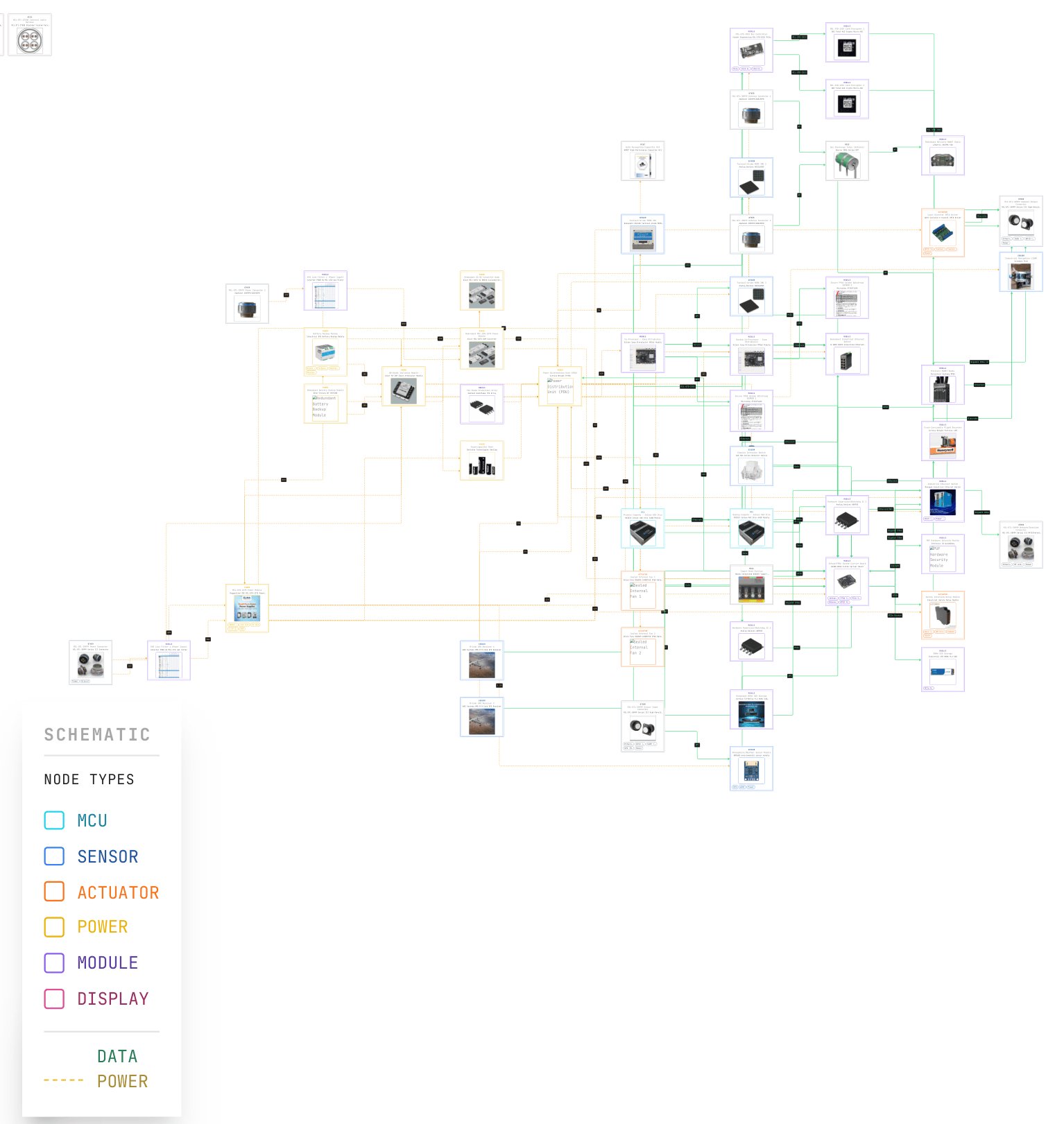
- Complete 9-module governance pipeline (SATA → ADARA → IFF → HMAA → MAIVA → FLAME → CARA → BDA → EFFECTOR) on edge hardware
- Dual-redundant compute architecture: NVIDIA Jetson AGX Orin + Xilinx Zynq UltraScale+ FPGA
- Physically hardwired normally-open safety interlock, weapon cannot fire without full pipeline authority
- Byzantine fault-tolerant swarm consensus over encrypted MANET mesh radio
- Multi-sensor deception detection across radar, EO/IR, LIDAR, GPS, IMU, and atmospheric sensors
- Production-path design: 72 components, MIL-STD-810G rated, ~$139K prototype (~$80K at scale)
Zenodo Publication: Oktenli, B. (2026). BLADE-EDGE: A Deterministic Governance Simulation Framework for Multi-Agent Decision Systems (5.0.3). Zenodo. https://doi.org/10.5281/zenodo.19177472