Framework Extension
Autonomous Drone Swarm Governance Platform
This project extends authority-governed autonomy from single-agent systems to coordinated multi-agent aerial platforms. Building directly on the rover and UAV testbeds, each drone operates as an individually governed autonomy node using SATA trust evaluation, HMAA authority control, and CARA recovery logic, while participating in a mission governed by a higher-level authority layer.
Unlike conventional swarm systems that assume continuous participation of all agents, this platform introduces trust-conditioned participation, where each drone's ability to contribute to the mission is dynamically constrained by its current trust and authority state.
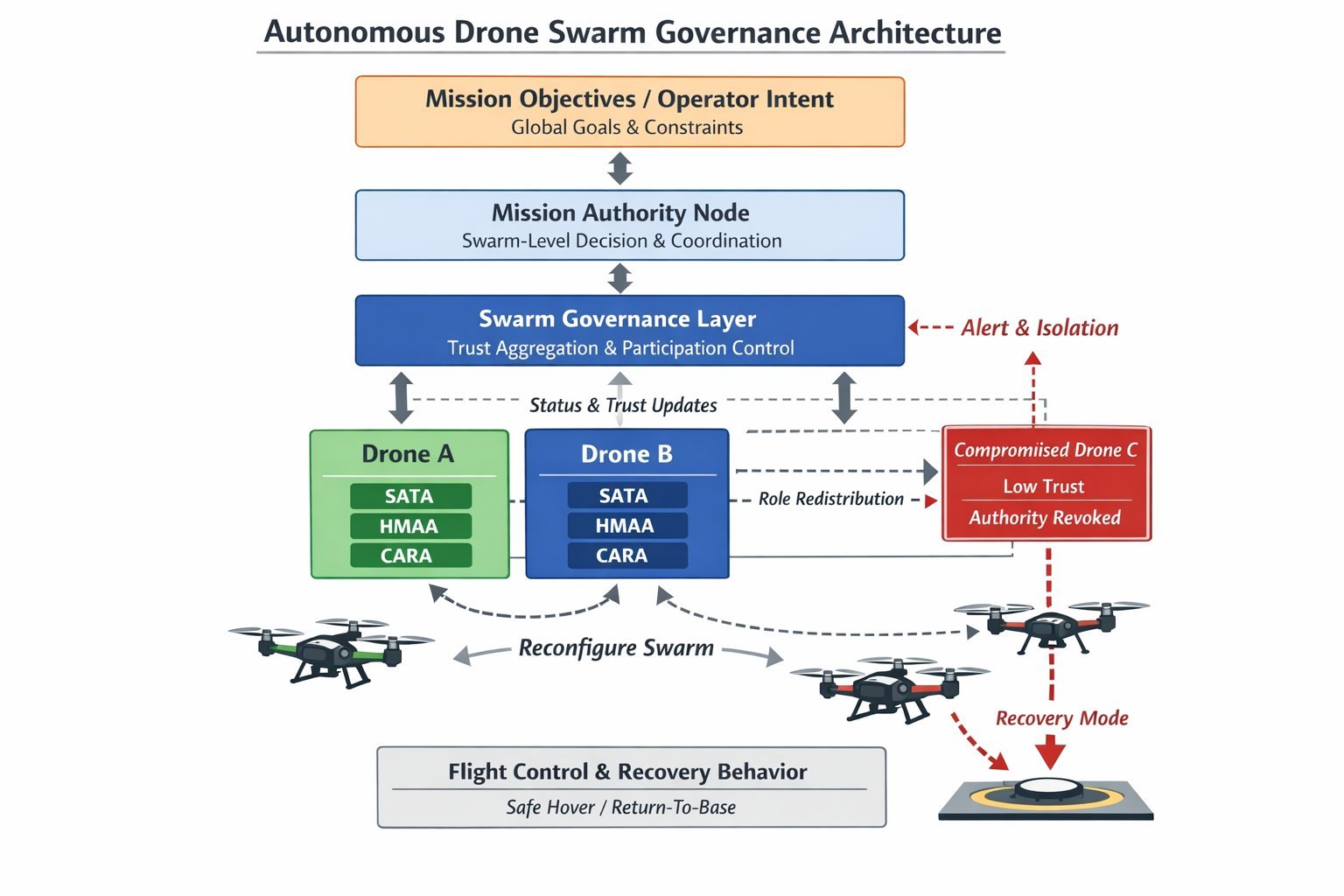
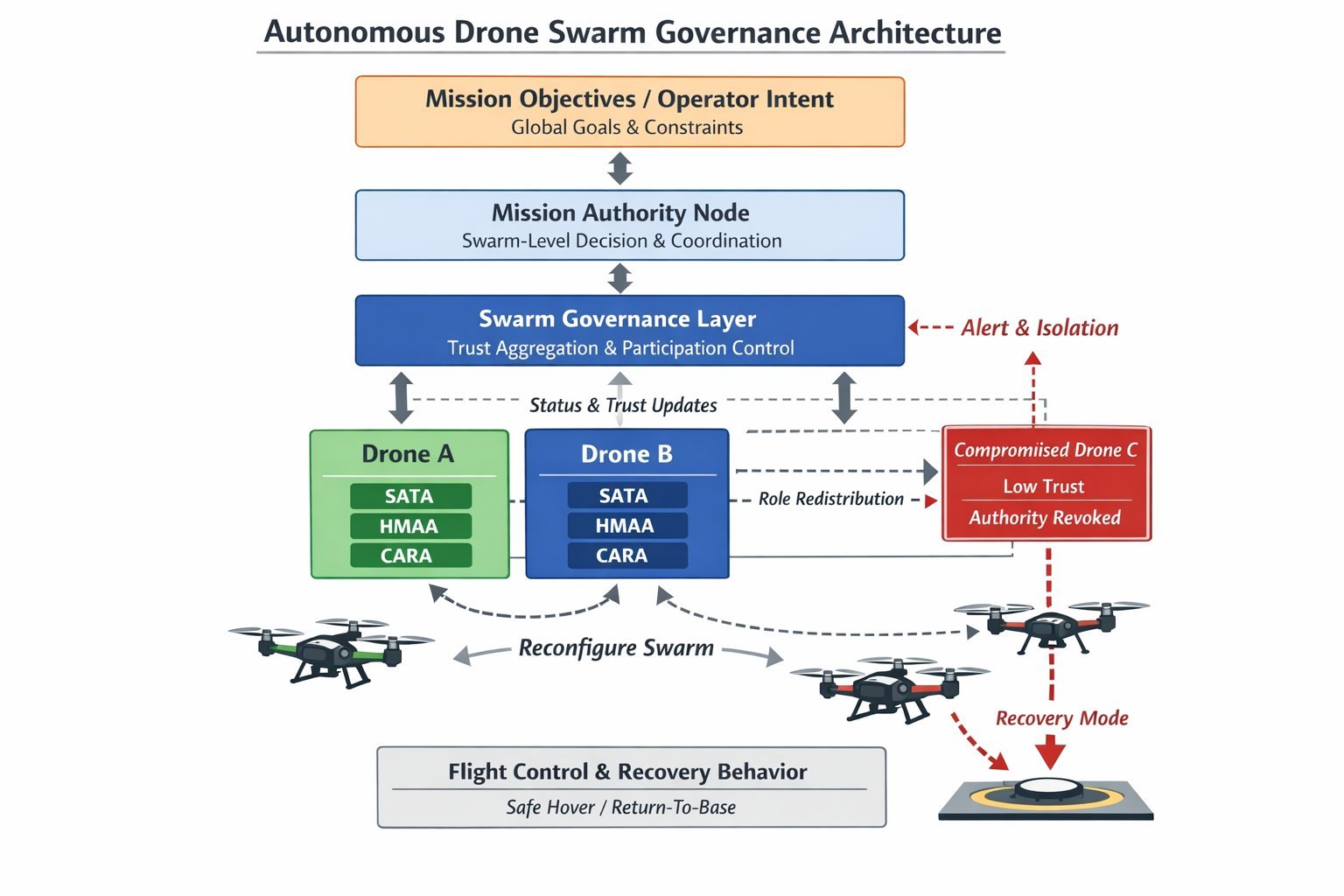
Figure 1. Autonomous Drone Swarm Governance Architecture. The system implements a multi-layer authority-governed autonomy framework in which mission objectives are translated into swarm-level decisions through a mission authority node and a distributed governance layer. Each drone operates as an independently governed autonomy node using SATA-based trust evaluation, HMAA authority computation, and CARA recovery enforcement. Local trust and status information are continuously propagated upward, enabling swarm-level trust aggregation and participation control. When a drone experiences trust collapse due to sensor inconsistency or adversarial interference, its authority is reduced or revoked, triggering isolation and recovery behaviors while the remaining agents dynamically reconfigure to maintain mission continuity.
Mission Objectives / Operator IntentGlobal mission goals and constraints
↓
Mission Authority NodeSwarm-level authority decisions and coordination policies
↓
Swarm Governance LayerDistributed trust aggregation, agent validation, participation control
↓
Per-Drone Governance NodesSATA trust evaluation, HMAA authority control, CARA recovery logic
↓
Drone Flight ControllersCommand execution constrained by authority and safety conditions
Dual-Layer Governance Model
Each drone continuously evaluates its own sensor trust and computes a local authority level. These local states are transmitted to the mission authority node, which evaluates swarm-wide conditions and determines whether individual drones may continue participating, must operate under constrained authority, or must be removed from the active mission.
Local Governance
Determines whether a specific drone can safely act based on its own sensor trust and authority state
Mission Governance
Determines whether a drone should continue contributing to the swarm based on fleet-wide trust conditions
Compromised Agent Response
- Sensor inconsistency or adversarial input triggers trust collapse on the affected drone
- HMAA reduces or revokes local authority for the compromised drone
- Mission authority node removes or restricts the drone's participation in the swarm
- Remaining drones dynamically reconfigure roles and formation
- CARA recovery initiates safe-hover, return-safe, or landing behavior on the isolated drone
Swarm Experimental Program
- Compromised Drone Isolation: Inject GPS spoofing on one drone. Measure trust collapse, authority revocation, swarm exclusion, and role redistribution among remaining agents.
- Swarm Degradation Under RF Loss: Remove multiple drones from communication. Measure mission continuity and objective reduction under reduced authority.
- False Consensus Defense: One drone reports incorrect position or threat data. Evaluate cross-agent trust disagreement detection and influence suppression.
- Recovery and Reintegration: Restore trust in a previously compromised drone. Measure controlled reintroduction under constrained participation before full authority restoration.
This platform demonstrates that authority-governed autonomy is not limited to individual systems, but can regulate coordinated autonomous teams operating under uncertainty, adversarial interference, and partial system compromise. The approach proposes a framework for swarm governance in which autonomy is continuously conditioned on trust, authority, and recovery state rather than assumed by default.
Research Summary
The proposed swarm governance platform extends authority-governed autonomy from single-agent systems to coordinated multi-agent environments. Each drone executes a local governance stack (SATA-HMAA-CARA) to evaluate sensor trust, compute authority levels, and enforce recovery behavior. These local authority states are integrated through a swarm governance layer that performs distributed trust aggregation and mission-level decision-making.
Unlike conventional swarm architectures that assume reliable participation of all agents, this system introduces trust-conditioned participation, where each drone's role in the mission is continuously evaluated and dynamically constrained. Compromised or unreliable agents are automatically isolated, while the swarm adapts by redistributing tasks among trusted drones. The architecture supports both degradation and recovery, enabling agents to be reintegrated under constrained authority once trust is restored.
"This work introduces authority-governed swarm autonomy, where each agent's participation is dynamically controlled based on trust, authority, and recovery state rather than assumed coordination."
This architecture addresses a critical gap in current autonomous systems, where multi-agent coordination lacks formal mechanisms for trust-aware participation control and structured recovery under adversarial conditions.
Realized as BLADE-SWARM
The swarm-governance concept proposed on this page is now formalized and implemented as the BLADE-SWARM Governance Node (DOI 10.5281/zenodo.20351198), the eighth BLADE platform. Where HMAA-UAV establishes the single-agent governance stack (SATA trust, HMAA authority, CARA recovery) on real flight hardware, BLADE-SWARM carries that same governance lineage forward to coordinated multi-agent swarms and develops the trust-conditioned participation model described above into a Byzantine-fault-tolerant two-phase consensus protocol.
BLADE-SWARM gates every swarm commit on SATA peer trust, the four-tier HMAA authority state, and weighted MAIVA voting; it tolerates up to f = (N-1)/3 compromised agents per quorum with a quorum-intersection safety bound, resists Sybil identities, and safe-halts by default under denied or degraded RF. Each node carries an ECDSA P-256 root of trust (ATECC608B) feeding a hash-chained distributed audit ledger, and the protocol is checked by a TLA+ formal specification (five safety invariants, three liveness properties) and a browser simulator across N = 10, 50, and 500 agents.
The two experiments proposed here map directly onto BLADE-SWARM validation scenarios: compromised-drone isolation under GPS spoofing corresponds to scenarios S2 (single Byzantine agent) and S3 (Sybil probe), and swarm degradation under RF loss corresponds to S4 (contested RF) and S5 (denied / degraded). The two platforms are designed to complement each other, HMAA-UAV as the single-node foundation and BLADE-SWARM as the multi-agent extension.