BLADE-INFRA Governance Node
BLADE-INFRA = Authority-Governed Critical Infrastructure Protection for ICS/SCADA
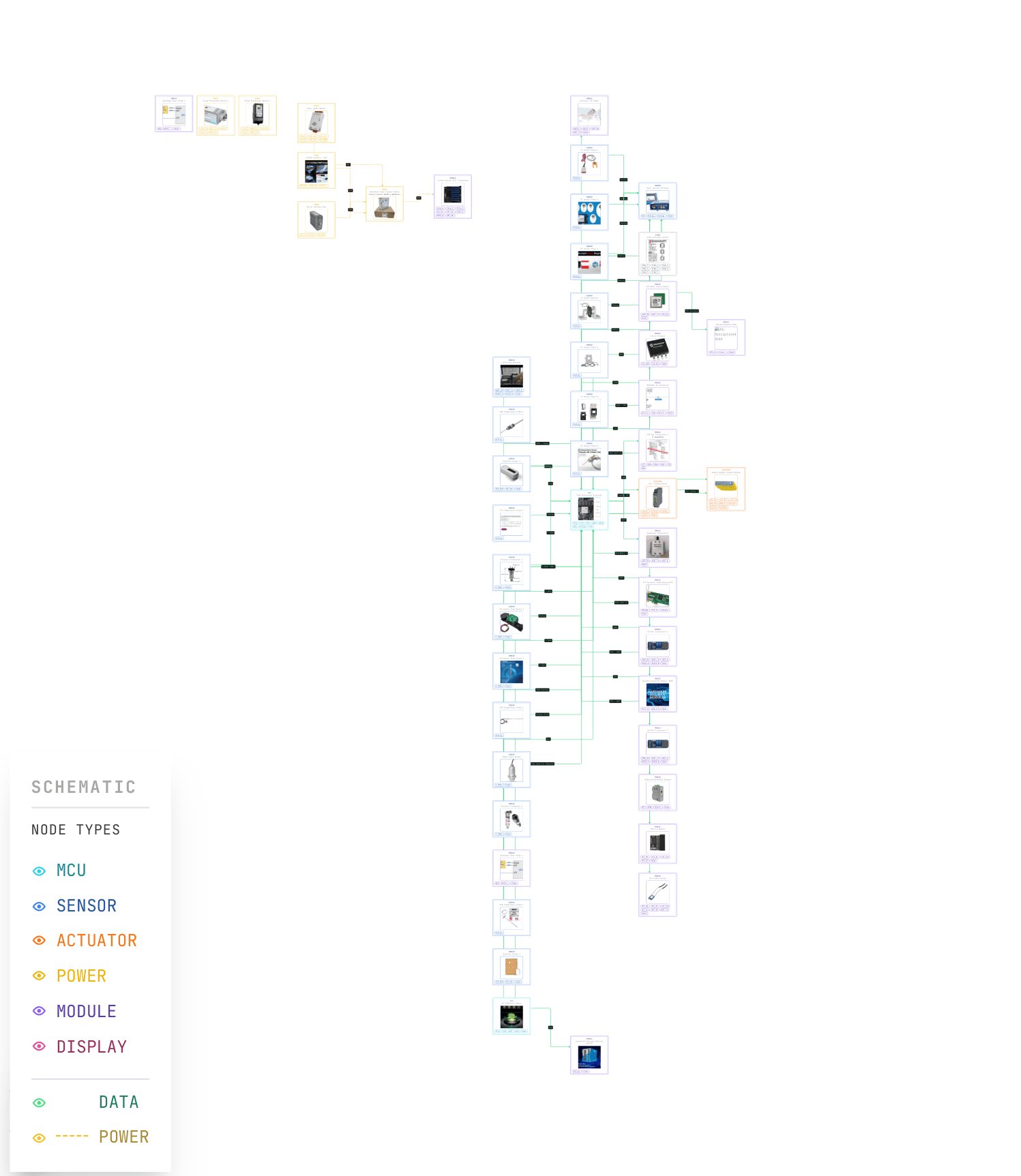
A ruggedized, authority-governed edge computing platform for critical infrastructure protection, ICS/SCADA monitoring, and industrial process control. Integrates Dempster-Shafer trust fusion, four-level authority with hysteresis, Byzantine fault-tolerant consensus, deliberation windows, and deterministic recovery, all enforced through a SIL-3 safety relay circuit driving a normally-open Pilz PNOZ S7.1 safety relay.
Published on Zenodo · DOI: 10.5281/zenodo.19277887This platform demonstrates that authority-governed autonomy is domain-agnostic: the same governance pipeline developed for defense applications in the BLADE-EDGE reference design applies directly to critical infrastructure systems under SIL 3 / IP65, NERC CIP, FIPS 140-2 Level 3, and IEC 62443 requirements.
Key Contributions
- 9-module authority-governed pipeline: SATA → ADARA → IFF → HMAA → MAIVA → FLAME → CARA → BDA → EFFECTOR
- Formal Dempster-Shafer trust fusion with binary frame Θ = {anomalous, nominal} with power quality, process, and environmental per-sensor mass functions
- SIL-3 dual-channel safety relay: Zynq PASS + Jetson APPROVE → Pilz PNOZ S7.1 (SIL 3, Cat. 4) dual-channel safety relay
- Dual-compute: NVIDIA Jetson Orin NX 16GB (AI/perception) + Zynq UltraScale+ ZU7EV (FPGA governance)
- Three ICS/SCADA governance scenarios with vintage CRT terminal live mode (v6.0, 98KB)
- IP65 / SIL 3 / NERC CIP target architecture with MIL-spec power chain (300W Vicor DCM5614, 32% margin)
- Cross-domain portability validated against BLADE-EDGE defense variant
Zenodo Publication: Oktenli, B. (2026). BLADE-INFRA Governance Node: Authority-Governed Critical Infrastructure Protection Node for ICS/SCADA Systems (v6.0). Zenodo. https://doi.org/10.5281/zenodo.19277887